The Kill Switch: Rendering Smartphones Useless to Thieves
People around the world use smartphones on a daily basis to interact with and store all kinds of data. In fact, according to Digital Trends, there are over 3.2 billion mobile devices currently in use. This boom in mobile technology has created a new wave of criminals, from hackers to street-level thieves, looking to make a quick buck off your devices and in some cases, your data.
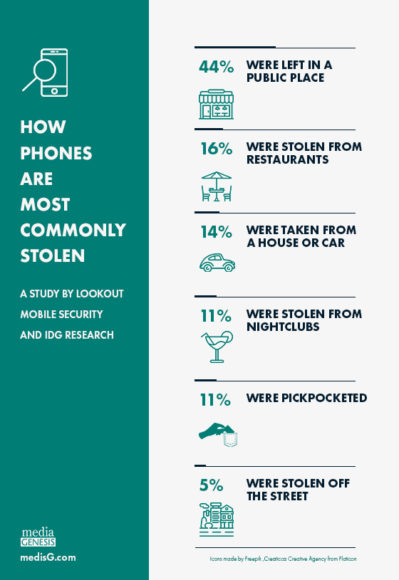
Smartphone theft has been on the rise in the U.S. According to a Harris poll, 10% of phone owners have had a phone stolen, and in 2012, 1.6 million Americans were victims of smartphone theft, according to Consumer Reports. According to a survey conducted by IDG Research and Lookout about 44% of phones are stolen from a public place, and about 11% were pickpocketed.
The good news? You’re not powerless against these malicious attacks.
Back Up Your Smartphone Data

Redundancy is the name of the game when it comes to keeping your smartphone data safe and secure. Smartphone devices hold some of our most valuable info such as messages, contacts, videos, and photos. It’s always a smart idea to keep your phone data backed up on a local computer or a cloud service.
Android devices can be backed up by syncing a Google account to the device. This will store wireless information, bookmarks, and text preferences, remotely on the Google servers. Locally storing text messages (SMS/MMS) requires third-party software, such as SMS Backup & Restore. Google’s store provides numerous applications to backup your phone’s data and other various settings.
Alternatively, photos and videos can be backed up simply through a USB connection to a local computer. From the computer, navigate to the phone’s photos folder, and drag the photos you want saved onto your computer.
Backing up all of the important documents, photos, and videos to a cloud service is also highly recommended. There are many cloud services available, but the most reliable and popular include: Google Drive, Dropbox, and Amazon Drive.
Apple devices promote their use of iCloud services to all of their users for storing information. They have made it completely customizable for users to choose their preferences and select what they back up. The entire iPhone can be backed up with the iCloud service if the user wants. Apple iPhone’s can also be backed up by connecting the device to a local computer. The iPhone is locally synced and backed up through iTunes. Under the device preferences section of iTunes users can back up iPhones, restore, or change backup settings.
All of my Data is Backed Up, Now What?
Backing up your data is the first step towards keeping it safe. With backed up data you have the security of knowing your phone can be lost or stolen, and the information is retrievable. However, this doesn’t keep you safe from remote security breaches.
Most commonly, hackers will use Spear Phishing, which uses public information to deceive you into releasing vital data. For example, using a disguised phone number, they will text you as a friend. These types of attacks are more strategically planned for high-profile individuals, but anyone is vulnerable.

To safeguard yourself from phishing or any other types of hacks on your device, you should:
- Keep the phone’s operating system up-to-date
- Never trust a text and/or email from unknown senders
- Don’t trust Public Wi-Fi with vital data
- Always request notifications when your account is logged into from an unknown device or when account information is updated
The Kill Switch: Lost or Stolen Smartphones
ChannelPro Networks states that 70 million mobile devices are lost or stolen each year.
Federal Communications Commission (FCC) chairman Tom Wheeler said “…smartphone theft remains a serious problem and that anti-theft tools only work if adopted widely.”
A collaborative effort between wireless companies and cell phone manufacturers such as Apple, Google, and Microsoft have adopted the kill switch ideology in order to aid against smartphone theft.
A majority of smartphone devices now come with pre-installed remote lock, erase, and restore tools. However, with privacy laws protecting the consumer, users can opt to disable these tracking and remote access capabilities. Smartphone users need to decide if these anti-theft tools are right for their situation.
Similar to a home alarm system, the kill switch protects the user by tracking, signaling, and in some cases disabling the device. However, users may need to sacrifice privacy for security. Nonetheless, anti-theft tools are a necessary measure in our smartphone present and future.
The kill switch is not the only way to protect your phone. You can also:
- Use PIN and Touch ID fingerprint to lock your phone when available. Ensure that your PIN is unique and not connected to any other accounts.
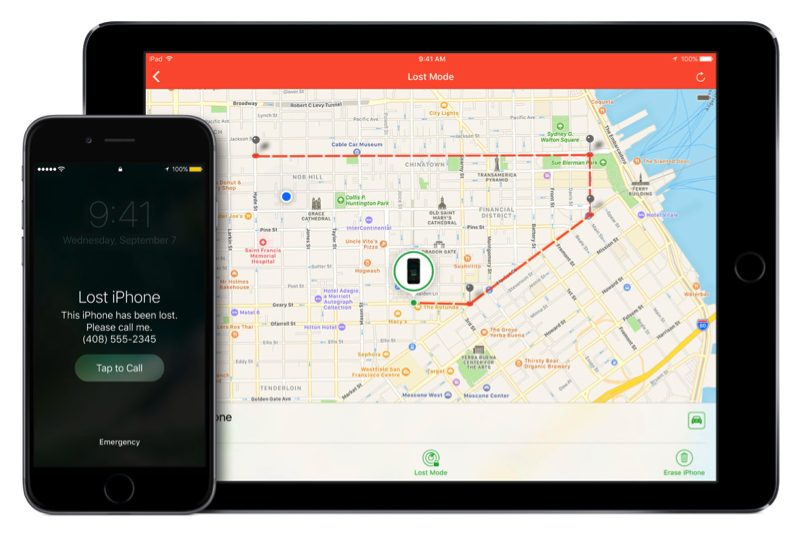
- Enable and activate the pre-installed Find My Device (Android) or Find My iPhone (Apple) applications. These apps allow the user to remotely alert, lock, wipe, or track the device.
- Keep all of the data backed up on a local computer.
- Backup all of the data on a remote cloud service.
Protect Yourself from Your Stolen Phone
If your device is stolen and there is no chance of recovering it, wipe it completely with remote Find My Device or Find My iPhone tools.
- Contact your phone provider and change all PINS and passwords.
- Contact all financial institutions and inform them of the stolen phone, and any fraudulent charges detected.
- Change all passwords, PINS, and two step authentication information for all services connected to your phone.
- Contact your local police department and file a report.
Need help protecting your company’s mobile data? Give us a call at 248.687.788 or email us at inquiry@mediag.com for more information on how we can help you keep your data safe and secure.


.png)
