Off the Hook: What You Need to Know About Phishing Scams and How Not to Be a Victim
By now, almost everyone has received an email from a Nigerian prince offering millions of dollars. You just had to send your password or bank information and he’d take care of the rest.
While not all scammers are that obvious, there are still plenty of “phishing” scams out there. The term phishing refers to the act of “fishing” for a victim’s password or financial and personal information on the internet by tricking them into thinking that you are someone or something else.
If you were ever unsure if an email you received from a company was real or if a website you were linked to had a legitimate URL, chances are attackers were trying to “phish” you.
Phishing, a Multi-Billion Dollar Business
The earliest noted occurrences of phishing were on America Online Instant Messenger (AIM). In 1995, phishers would pose as AOL employees, requesting a user’s billing information via IM. By 2001, the phishing attacks expanded to payment systems, such as PayPal. Since the earliest days of phishing, the methods haven’t changed very much.
In 2015 the Anti-Phishing Working Group (APWG) collected 1,413,978 reported phishing attacks. In 2014, the APWG estimated $5.9 billion in losses connected to phishing. The majority of financial loss due to phishing is through corporate oversight.
There are numerous forms of phishing used to exploit individuals into releasing personal information. Commonly, attackers will use “spear phishing,” which uses public information as a tool for social-engineering attacks. This type of attack will use trustworthy appearing email addresses to deceive the individual. Phishing attacks frequently target information for bank institutions, credit cards, and social media credentials.
The Types of Phishing
There are three main types of phishing attacks: spear, clone, and whaling.
Spear Phishing: Spear phishing will use public information to deceive an individual into revealing their passwords or financial information.
Clone Phishing: This method uses the attachments and contents of a legitimate email and extends it to cloned images, text, and even entire websites. With Clone Phishing the goal is to acquire information via a login screen or email interaction.
The spoof website will be an exact clone of the legitimate website. The spoof domain can use URL redirects to deceive the user. Redirects are used to make the trustworthy domain appear in the address bar, but malicious websites are directed in the background. For example, attackers can use JavaScript to alter the appearance of the address bar. The legitimate content will display and the attacker has the malicious website load in another tab, or use the JavaScript to cloak the malicious address.
Whale Phishing: One of the more uncommon types of phishing attacks, whale phishing is often the most costly due to sizable financial losses. This type of phishing is targeted at a larger profile individual. With access to public information, these attackers will use social engineering to deceive the individual or company. For example, the attacker will gain access to an employee email account, which is used to deceive an executive about an accounting issue.
How to Spot a Fake Email
Below is an example of a phishing email, see if you can identify the four issues.
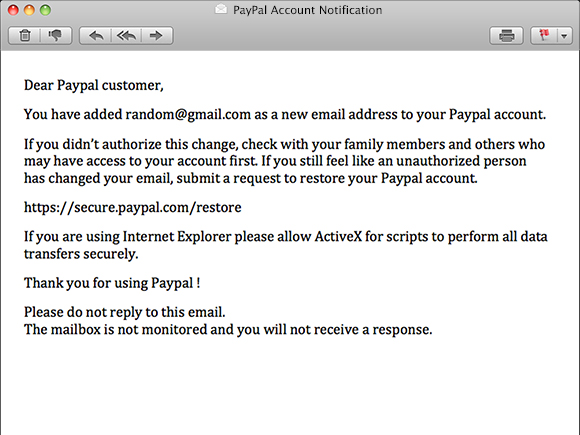
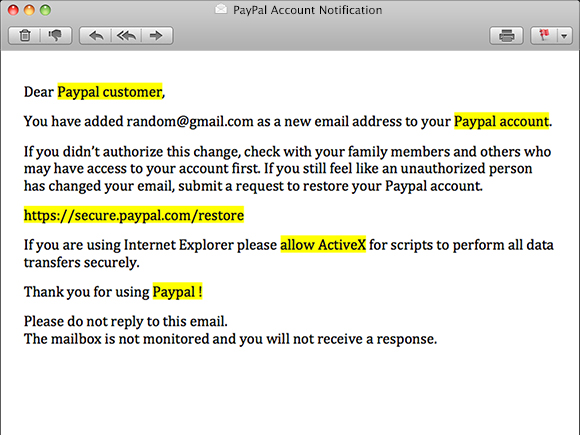
1) Generic Terms
The above email is using generic terms, such as “Dear Paypal customer”. It is uncommon for a legitimate organization to not use a customer’s actual name. If you have an account, sources such as PayPal will reference your name.
2) Fear Vs. Facts
By hinting that the user’s account was compromised, the attacker has developed fear. Using terms such as “unauthorized,” “restore,” and “securely” provide the problem and solution.
3) Beware of Links
The email references a link as the solution; this link and website will appear to be legitimate. In actuality, it’s the main attraction to the phishing attack.
4) Misuse of the Company Name
The last indication of a phishing attack is the use of a trustworthy organization’s name throughout the email. Generally, attackers will use versions of “Paypal,” “Pay-Pal,” and “paypal” to bypass anti-phishing technologies. Referencing legitimate PayPal emails, they will always use “PayPal” as their company name.
Reference the email below to see the issues we listed above;
How to Spot an Imposter
Even if two pages look identical, there are several methods to seek out a phishing website.
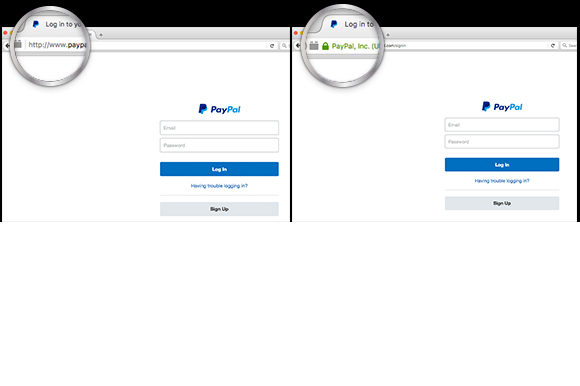
If you were previously logged into a website, such as PayPal, the credentials will commonly save. On most redirects, cloaks, or clones you won’t see an SSL certificate on the address bar.
Websites such as PayPal will always use HTTPS prefixes before their entire URL. Nonetheless, some phishing attacks have been able to appear legitimate with an SSL certification. The best method to prevent domain manipulation is to always type the website directly into the browser yourself.
How to Protect Yourself
Use the following precautions to protect yourself from phishing scams:

Phishing for data is considered big business; but people are fighting back. Now, you can hire professional hackers to help you protect yourself. Public awareness of these types of attacks has risen, but as technologies advance the public needs more training to resist an attack. We all need to be aware of the generic terminology, domain manipulation, and cloned content.
Need help protecting your company’s data and information? Give us a call at 248.687.788 or email us at inquiry@mediag.com for more information on how we can help you be safe.


.png)
